Takeways
Wireless network security refers to technologies, protocols, and practices that protect wireless networks and data from unauthorized access and cyber threats.
It prevents data breaches, unauthorized access, and service disruptions, as wireless signals can be intercepted without physical access.
It combines encryption, authentication, access control, and continuous monitoring to secure network access and data transmission.
The main protocols are WEP (obsolete), WPA, WPA2 (outdated), and WPA3 (recommended), with each generation offering stronger encryption and authentication.
Common threats include unauthorized access, data interception, and exploitation of protocol or device vulnerabilities.
Common attacks include deauthentication, evil twin access points, man-in-the-middle, packet sniffing, replay, and denial-of-service attacks.
Use WPA3 encryption, network segmentation, intrusion detection, regular updates, physical security, and user education.
Future trends include WPA3 adoption, Zero Trust architecture, AI-driven detection, IoT protection, and adaptive risk-based security models.
What Is Wireless Network Security?
Wireless network security refers to the technologies, protocols, and practices designed to protect wireless networks and the data transmitted over them from unauthorized access, interception, and cyber threats. Its primary objective is to ensure that only authorized users and devices can connect to the network, while maintaining the confidentiality, integrity, and availability of data.
Why Is Wireless Network Security Important?
As organizations increasingly rely on wireless connectivity, the attack surface expands significantly. Unlike wired networks, wireless signals can be intercepted without physical access, making them inherently more exposed to threats.
Without proper protection, wireless networks can lead to:
- Data breaches involving sensitive business or customer information
- Unauthorized access to internal systems
- Service disruptions that impact business operations
- Compliance risks in regulated industries
For enterprises, securing wireless infrastructure is no longer optional but a foundational requirement for overall cybersecurity.
How Does Wireless Network Security Work?
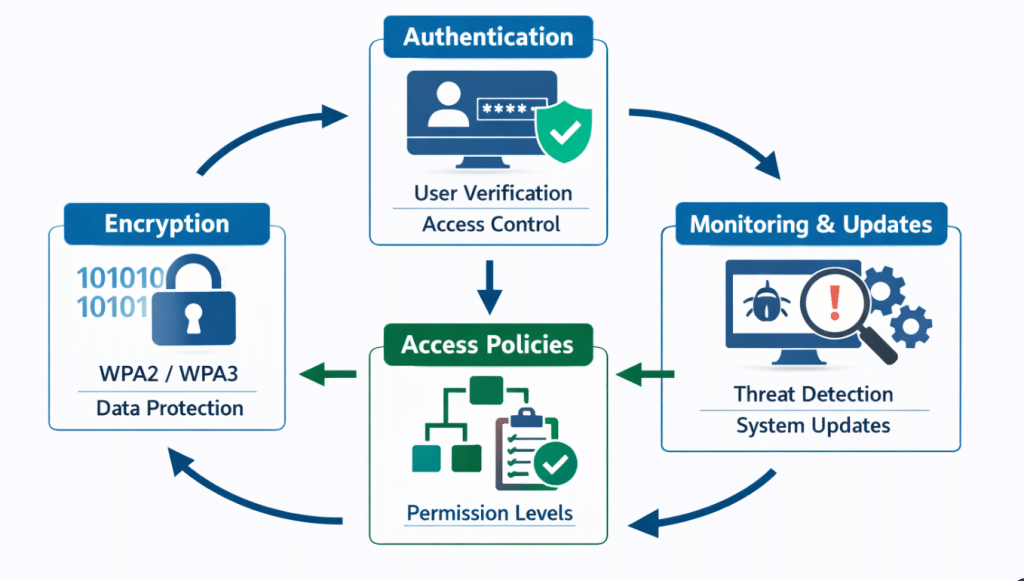
Wireless network security operates through a combination of technical mechanisms that work together to safeguard both network access and data transmission.
At the core of this system is encryption, which protects data as it travels between devices by converting it into a form that cannot be easily interpreted by unauthorized parties. Modern standards such as WPA2 and WPA3 are widely used to provide this protection.
Authentication mechanisms ensure that only verified users or devices are allowed to connect, typically through credentials or identity-based validation. Once access is granted, access control policies define the level of permissions available within the network.
In addition to these foundational elements, security also depends on ongoing management and monitoring. Network devices must be regularly updated to address vulnerabilities, and protective tools such as intrusion detection and prevention systems continuously analyze traffic to identify and respond to suspicious activity in real time.
What Are the Main Types of Wireless Network Security Protocols?
The four main types of wireless network security protocols—WEP, WPA, WPA2, and WPA3—represent the evolution of wireless protection standards over time. Each protocol introduces improvements in encryption, authentication, and resistance to emerging attack methods.
1. WEP (Wired Equivalent Privacy) – 1997
WEP was the first security protocol designed to protect wireless networks. It uses 40-bit or 104-bit encryption keys and relies on the RC4 stream cipher for data encryption. However, its use of static keys and weaknesses in the initialization vector design make it highly vulnerable to attacks.
As a result, WEP is now considered obsolete. Modern networks no longer use it, as attackers can compromise WEP-protected systems within minutes using widely available tools.
2. WPA (Wi-Fi Protected Access) – 2003
WPA was introduced as an improvement over WEP, addressing many of its critical vulnerabilities while maintaining compatibility with older hardware. It uses the Temporal Key Integrity Protocol (TKIP), which dynamically generates new encryption keys for each data packet.
WPA also supports both personal and enterprise authentication modes, improving flexibility. However, it was designed as a transitional solution, and certain cryptographic limitations mean it no longer meets modern security requirements.
3. WPA2 (Wi-Fi Protected Access 2) – 2004
WPA2 significantly strengthened wireless security by replacing TKIP with the Advanced Encryption Standard (AES), offering more robust data protection. It uses CCMP for encryption and supports both personal (pre-shared key) and enterprise (RADIUS-based) authentication methods.
Due to its strong encryption and broad compatibility, WPA2 became the industry standard for many years. However, vulnerabilities such as key reinstallation attacks (KRACK) have shown that even widely adopted protocols are not immune to evolving threats.
4. WPA3 (Wi-Fi Protected Access 3) – 2018
WPA3 is the latest wireless security protocol, designed to address the limitations of earlier standards. It introduces Simultaneous Authentication of Equals (SAE), which enhances password-based authentication and protects against offline brute-force attacks.
| Feature | WEP (1997) | WPA (2003) | WPA2 (2004) | WPA3 (2018) |
| Encryption Cipher | RC4 (Stream) | TKIP (RC4-based) | AES-CCMP (Block) | AES-GCMP (stronger) + GCMP-256 (Wi-Fi 7) |
| Key Length | 40/104-bit + 24-bit IV | 256-bit (dynamic) | 128-bit (AES) | 192-bit / 256-bit options |
| Authentication | Open / Shared Key (static) | PSK (Personal) / Enterprise | PSK (Personal) / 802.1X (Enterprise) | SAE (Personal) / 802.1X + enhanced (Enterprise) |
| Offline Brute-Force Resistance | None (cracked in minutes) | Weak | Moderate (vulnerable with weak passwords) | Strong (SAE protects against offline attacks) |
| Forward Secrecy | No | No | No | Yes |
| Protected Management Frames (PMF) | No | No | Optional | Mandatory |
| Open Network Encryption | None | None | None | OWE (Enhanced Open) supported |
| Vulnerabilities | Extremely high (static keys, IV reuse) | TKIP weaknesses, offline attacks | KRACK, dictionary attacks | Much fewer; side-channel issues rare |
| Current Status (2026) | Obsolete – Never use | Obsolete – Avoid | Still common but outdated | Recommended / Mandatory for Wi-Fi 7 |
| Best Use Case | None | Legacy compatibility only | Mixed environments with old devices | All modern home & enterprise networks |
In enterprise environments, WPA3 supports stronger encryption standards, while also providing forward secrecy to ensure that previously captured data cannot be decrypted even if credentials are later compromised. Despite these improvements, adoption has been gradual due to compatibility and deployment challenges.
What Are Common Threats to Wireless Networks?
Wireless networks are exposed to a range of threats that exploit both technical vulnerabilities and the open nature of wireless communication. These threats can affect different stages of network interaction, from initial access to ongoing data transmission.
Common examples include:
- Unauthorized access, where attackers gain entry to a network without permission, potentially leading to data theft, misuse of resources, or further system compromise
- Data interception, which involves monitoring wireless communication to capture sensitive information, especially when encryption is weak or improperly configured
- Cyber exploits, where attackers take advantage of vulnerabilities in wireless protocols, devices, or network architecture to disrupt services or gain control
In practice, these threats are often interconnected. For example, an attacker may first gain unauthorized access and then proceed to intercept data or exploit system weaknesses. This layered nature of attacks highlights the importance of implementing comprehensive and well-maintained security measures.
What Are the Common Types of Wireless Network Attacks?
Wireless networks are exposed to specific attack techniques that exploit vulnerabilities in protocols, devices, or user behavior. Some of the most common types include:
- Deauthentication and disassociation attacks: Attackers force devices to disconnect from a legitimate network, often to capture authentication data or redirect users to malicious access points.
- Rogue or “evil twin” access points: Malicious networks mimic legitimate ones to trick users into connecting. Once connected, attackers can intercept sensitive data or inject malicious traffic.
- Man-in-the-middle (MITM) attacks: Attackers position themselves between the user and the destination server to intercept, modify, or inject data.
- Packet sniffing and eavesdropping: Monitoring wireless traffic to capture sensitive information, particularly when encryption is weak or absent.
- Replay attacks: Previously captured packets are retransmitted by an attacker to gain unauthorized access or manipulate network behavior.
- Denial-of-service (DoS) attacks: Attackers flood the network or exploit protocol weaknesses to disrupt normal operation.
Often, attackers combine multiple techniques to increase their impact. Understanding these attack types is critical to designing effective defenses.
How Can Wireless Network Attacks Be Defended Against?
Defense against wireless network attacks requires both proactive and reactive strategies. Key measures include:
- Strong encryption and authentication: Using WPA3 and enforcing strong password policies protects data and prevents unauthorized access.
- Network segmentation and access control: Separating networks by device type or user group limits the potential impact of an attack.
- Intrusion detection and prevention systems (IDPS): Monitoring network traffic for anomalies can detect rogue access points, MITM attempts, and other suspicious activities.
- Physical security measures: Restricting access to routers, access points, and other network devices prevents tampering.
- User education and awareness: Teaching users to recognize suspicious networks and avoid insecure behaviors reduces social engineering risks.
- Regular updates and patch management: Keeping firmware, devices, and security software up to date minimizes exposure to known vulnerabilities.
Combining these strategies creates a multi-layered defense that addresses both technical and human factors.
What Are the Future Trends in Wireless Network Security?
As wireless environments become more complex and distributed, the nature of security is shifting from perimeter-based protection to continuous, context-aware risk management. Traditional controls such as encryption and authentication remain essential, but they are increasingly insufficient on their own.
Several key trends are redefining how wireless networks are secured:
WPA3 Adoption and the Evolution of Encryption Standards
The transition from WPA2 to WPA3 marks a broader shift toward stronger, more resilient cryptographic protections. Beyond improved encryption, WPA3 introduces mechanisms such as forward secrecy and resistance to offline brute-force attacks.
However, adoption remains uneven due to legacy device compatibility, meaning many environments must operate in mixed-mode deployments—creating potential security gaps that attackers can exploit.
Zero Trust Architecture Extending to Wireless Networks
The traditional assumption that devices within a network can be trusted is being replaced by the principles of Zero Trust Architecture, a concept from National Institute of Standards and Technology (NIST).
In wireless environments, this means:
- Continuous authentication of users and devices
- Context-aware access decisions based on identity, device posture, and behavior
- Minimization of implicit trust, even within internal networks
This approach is particularly important as remote work and BYOD (bring your own device) models expand.
AI-Driven and Behavior-Based Threat Detection
As attack techniques become more automated and adaptive, static rule-based detection is no longer sufficient. Organizations are increasingly leveraging machine learning to:
- Identify anomalous traffic patterns
- Detect previously unknown attack signatures
- Correlate events across network layers in real time
This shift reflects a move toward behavior-based security, where deviations from normal activity become a primary signal of compromise.
The Expanding Attack Surface of IoT Devices
The rapid growth of IoT devices introduces significant security challenges. Many of these devices:
- Lack robust built-in security controls
- Use outdated firmware that is rarely patched
- Operate with limited visibility within network monitoring systems
As a result, IoT endpoints are becoming a primary entry point for attackers, requiring more granular segmentation, device identification, and continuous monitoring.
Convergence of Network and Application-Layer Security
A critical shift in modern security strategy is the recognition that network-level protection alone cannot fully mitigate risk.
Even in well-secured wireless environments:
- Valid credentials can be stolen or abused
- Encrypted traffic can still carry malicious payloads
- Trusted sessions can be hijacked or automated
As a result, organizations are increasingly integrating network security with application-layer controls, focusing not only on whether access is granted, but also on how that access is used.
From Reactive Defense to Adaptive Security Models
Perhaps the most significant trend is the transition from reactive security to adaptive, risk-based models. Rather than relying solely on predefined rules, modern systems continuously assess risk based on multiple signals, including:
- User behavior
- Device characteristics
- Access patterns
- Environmental context
This enables more dynamic responses, such as step-up authentication, session monitoring, or real-time access restriction.
Conclusion
Looking ahead, the integration of Zero Trust principles, AI driven threat detection, and better protection for IoT devices will shape the next generation of wireless defense. Organizations must move beyond static protections toward adaptive, risk based security models that respond dynamically to emerging threats.
The message is clear. Do not wait for a security incident to reveal weaknesses in your wireless infrastructure. Assess your current Wi Fi setup, prioritize migration to WPA3, implement network segmentation, and adopt forward thinking security practices.
By investing in strong wireless network security today, you safeguard your data, protect your operations, and build resilience for an increasingly wireless future.